10 Devastating OWASP Flaws That Hackers Exploit in 2026
Every year, thousands of websites and applications get breached not through sci-fi zero-days, but through the same predictable, well-documented flaws.

Every year, thousands of websites and applications get breached not through sci-fi zero-days, but through the same predictable, well-documented flaws.

Imagine receiving a video call from what appears to be a police officer, complete with uniform and official backdrop, demanding

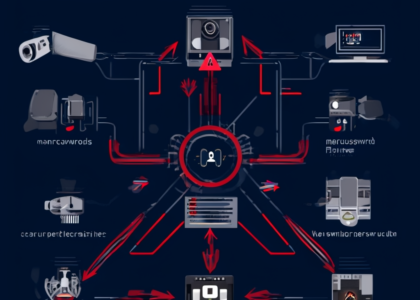
The Rise of AI-Powered Cyberattacks Artificial intelligence has transformed cybersecurity from both sides of the battlefield. While businesses leverage AI

The alarming reality is that 94% of web applications have security vulnerabilities that could expose sensitive data or enable unauthorized
Top Cybersecurity Trends & Threats in 2025 As we move further into the decade, understanding the top cybersecurity trends 2025

Step-by-Step Guide to Your First Bug Bounty Program Bug bounty hunting is an exciting way for students and aspiring ethical

Simple Steps to Protect Your Personal Data from Hackers Introduction In an era where cyber threats are constantly evolving, learning