Your startup moves fast. It ships fast. But are you sure it is shipping securely? DevSecOps is the absolute best way to protect your code. Therefore, you must start building it from day one.
Speed without security is a massive risk today. For example, hackers find new weak spots incredibly fast. Sometimes, they attack a new vulnerability in under 24 hours. Despite this reality, many startups delay their security completely. Consequently, they wait until a major breach happens to take action.
Ultimately, this delay costs startups millions of dollars. Fortunately, you can avoid this nightmare entirely. This guide explains DevSecOps clearly and simply. Specifically, we cover exactly what it is and why it matters. Furthermore, we show exactly how to build it today. Thus, you can stay completely safe on a tight bootstrap budget.
What is DevSecOps?
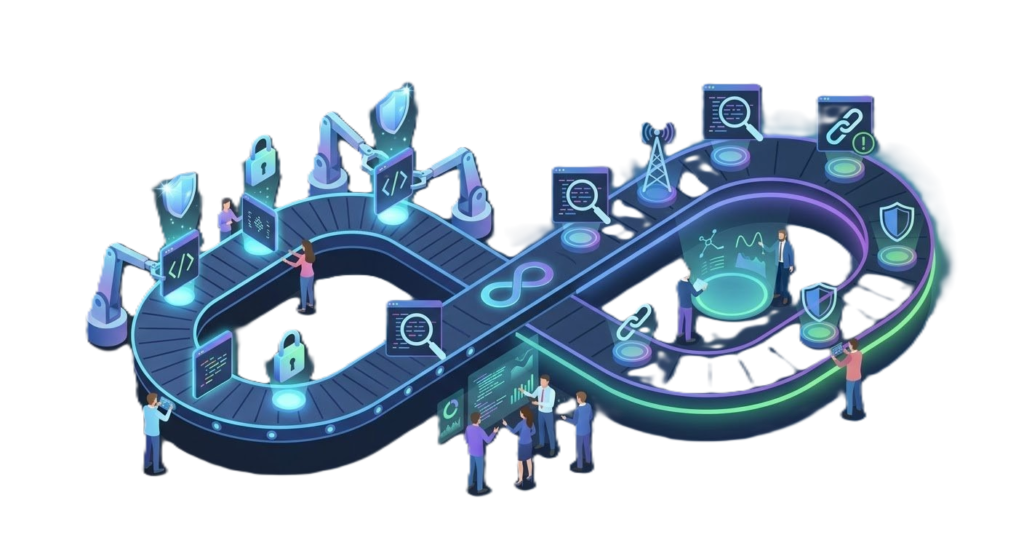
DevSecOps means Development, Security, and Operations. Primarily, it shifts how modern software teams view security. In the past, teams tested security last. First, developers wrote code. Next, they built features. Finally, they checked for flaws.
As a result, this traditional method caused expensive and dangerous problems. DevSecOps fixes this core issue. Instead of waiting, it weaves checks directly into your daily work. Thus, testing starts immediately. Afterward, it continues all the way to production.
In fact, traditional testing is like painting a finished house. Conversely, DevSecOps is like steel framing inside concrete. Therefore, it is structural, vital, and highly effective.
Key Definition
DevSecOps integrates security everywhere. Specifically, it uses automation to enforce strict rules. Thus, you catch flaws instantly at the source instead of in production.
The Shift-Left Philosophy
“Shifting left” moves security earlier in the project timeline. Therefore, developers do not wait for external auditors. Instead, they catch issues during the initial design phase. Why does this matter? Primarily, fixing bugs gets vastly more expensive over time.
For example, catching a flaw early costs very little. Conversely, finding an error after launch is totally devastating. Therefore, shifting left is an excellent strategy. Furthermore, it saves massive amounts of money. Ultimately, it protects your brand reputation entirely.
| Stage of Discovery | Relative Cost to Fix |
|---|---|
| Design Phase | ~$80 |
| Coding Phase | ~$240 |
| Integration / Testing | ~$960 |
| Post-Release | $96,000+ |
Why DevSecOps is Vital
Many founders ignore security entirely. However, this is a dangerous and costly mistake. In fact, small businesses face many severe attacks daily. Attackers target them specifically because they have weak defenses.
Startups face unique and massive risks. For instance, they push code quickly. Additionally, they use many open-source tools. Consequently, this creates a perfect storm for hackers. Therefore, a secure pipeline is absolutely mandatory.
The Rise of AI Threats
Furthermore, AI threats are growing incredibly fast. Thus, hackers find open network ports in minutes. Therefore, your fix window is completely gone. You can read more about this grim reality in our detailed guide on 2026 AI cyber threats.
Moreover, developers often use risky automation tools secretly. As a result, they expose private company data blindly. We explain this danger deeply in our post about hidden shadow AI threats. Thus, you must stay extremely vigilant.
Front-End DevSecOps
Many teams completely ignore front-end code. However, this is totally wrong. Modern front ends hold highly secure tokens. Moreover, they talk to background APIs directly. Thus, they create huge risks that hackers exploit constantly.
Top Front-End Targets
First, attackers use cross-site scripting to steal session cookies. Next, they exploit bad API calls to view private data. Then, they steal exposed API keys right from your code. Furthermore, bad dependency chains ruin everything. Finally, weak logins cause total account breaches.
Security Mandate
Therefore, your pipeline must scan absolutely everything. Indeed, UI code is never low-risk. You must protect it aggressively.
A DevSecOps Case Study
Let us look at a real example. FinStack was a small fintech company. Initially, they handled security manually. However, a deep audit found three critical flaws.
First, a secret cloud key sat in a public folder. Next, their invoice tool had a bad access bug. Finally, a chart tool had a known script flaw. Consequently, any of these items could ruin them instantly.
How They Fixed It
First, they used GitLeaks immediately. Thus, they found hidden keys fast. Next, they added Semgrep to their tools. Therefore, they scanned new code automatically. Then, they used Burp Suite testing. As a result, they found complex access bugs.
Finally, they set up Nmap. Thus, they monitored network ports weekly. Ultimately, they passed their big security review easily. Furthermore, they signed a massive new enterprise client.
Essential DevSecOps Tools
You do not need a huge budget. In fact, many great tools are entirely free.
| Tool | Purpose |
|---|---|
| GitLeaks | Secret detection (Free) |
| Semgrep | Code scanning (Free tier) |
| Snyk | Dependency checks (Free) |
| Burp Suite | Web testing (Free tier) |
| Trivy | Container scanning (Free) |
Thus, every team should read the OWASP Top 10 guidelines carefully. They are incredibly helpful. Furthermore, they outline the biggest web risks clearly.
Implementing DevSecOps Fast
Founders often say they lack money for security. However, DevSecOps solves this exact problem perfectly. Specifically, it automates the hard manual work. Thus, it saves you immense time and resources.
Focus on Quick Wins
First, you must focus on immediate victories. For example, enable GitHub secret scanning today. This takes only five minutes. Consequently, you instantly protect your code repository. Next, add pre-commit hooks everywhere. Therefore, developers cannot upload bad keys by mistake. Then, run an npm audit immediately. As a result, you find outdated packages fast. Finally, restrict all cloud accounts. Thus, you limit internal damage.
Plan Your Next Steps
Furthermore, you must plan your next steps carefully. Next, integrate Trivy into your container builds. Therefore, you stop vulnerable images completely. Afterward, test everything dynamically using automated scanners. Additionally, you should train your developers regularly. Consequently, they will write safer code naturally over time. For a larger plan, review the NIST Cybersecurity Framework to map your entire progress.
The DevSecOps Starter Checklist
Use this simple checklist today. Share it with your lead engineer immediately. Thus, your whole team aligns on security goals.
- Step 1: First, secure your secrets in a centralized vault. For instance, never hardcode passwords in your files. Consequently, attackers cannot scrape your private data.
- Step 2: Next, scan all dependencies safely. Specifically, monitor your software supply chain constantly. Therefore, block any critical flaws from merging.
- Step 3: Then, test code statically using strict rules. Furthermore, integrate these alerts directly into developer tools. As a result, engineers fix bugs while typing.
- Step 4: Afterward, test dynamically on staging environments. Thus, you catch complex runtime errors early. Furthermore, document every single finding clearly.
- Step 5: Finally, harden your cloud access strictly. Indeed, you must scan infrastructure templates regularly. Ultimately, this stops dangerous cloud misconfigurations entirely.
Common DevSecOps Vulnerabilities
Your pipeline must stop known risks systematically. Specifically, attackers look for these exact flaws constantly. You can learn how they exploit them in our article on devastating OWASP flaws. Therefore, understanding these threats is highly important.
| Vulnerability | Control Strategy |
|---|---|
| Injection Flaws | Implement SAST rules and filter inputs closely. |
| Broken Auth | Force MFA enforcement and test session limits. |
| Data Exposure | Run secret scanning on every single code commit. |
| IDOR | Perform API fuzzing and manual logic testing. |
Meeting Compliance with DevSecOps
DevSecOps improves your compliance posture fast. In fact, new international laws demand strict security. Fortunately, every automated test acts as legal proof. You can learn about the complex new rules in our post on 2026 cybersecurity regulations.
For example, SOC 2 certification needs tight access logs. Thus, your pipeline makes them automatically during builds. Similarly, PCI DSS requires fast dependency updates. Therefore, automated security tools handle this requirement easily.
Startups using these methods finish audits much faster. Consequently, passing an enterprise audit is simple. Furthermore, investors love companies that prioritize compliance early. Thus, it makes fundraising significantly easier.
Conclusion
Adding security early is a brilliant move. Indeed, it is your absolute best business investment. For example, automated scanning tools cost very little. Conversely, a major data breach costs millions of dollars. Therefore, DevSecOps saves your entire business from disaster.
Furthermore, it builds massive trust with your customers. Consequently, massive enterprise clients will buy your software faster. Moreover, your engineers will feel much happier daily. Thus, they will ship code with total confidence. Ultimately, you cannot survive modern cyber threats without it. Start building your secure pipeline today.
Ready to Audit Your Security?
Reading about DevSecOps is only step one. Do you truly know your current weak spots? Sadly, most startup founders do not know at all. Consequently, malicious hackers find these hidden gaps first.
Cybknow Technologies offers incredible web penetration testing. Specifically, we find your exact security gaps fast. Next, we help your development team fix them permanently. First, we map your entire attack surface carefully. Then, we simulate real hacker attacks safely on your staging environments.
Afterward, we deliver a highly clear remediation roadmap. Therefore, your developers know exactly what to do next. Furthermore, we test everything again to verify the fixes. Thus, you stay completely safe and secure continuously. Stop guessing about your cybersecurity posture today.